8. Vocabulary¶
8.1. Tenant¶
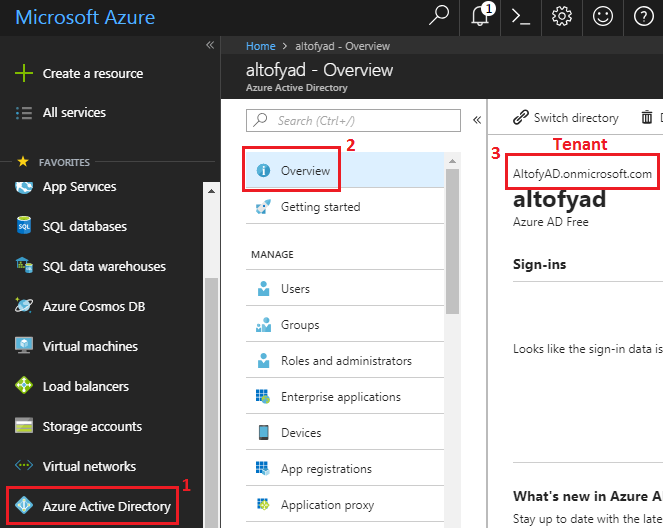
A “Tenant” is representative of an organization. “Tenant” string is in format:
<YourDirectoryName>.onmicrosoft.com
Each “Tenant” is distinct and separate from other Azure AD tenants and it’s without https:// at the beginning.
See figure below to find how to obtain your directory name.
In this case “Tenant” is: altofyad.onmicrosoft.com.
8.2. Tenant ID¶
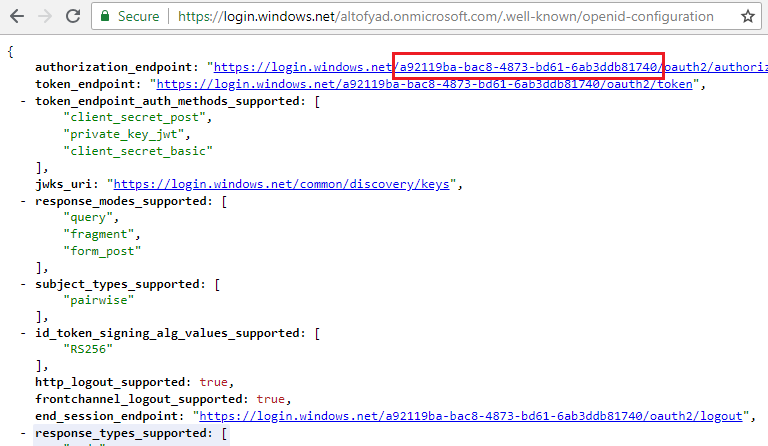
“TenantID” is a unique number that is representing your Azure AD organization. To get the “TenantID”, download a JSON file that is located at:
https://login.windows.net/<YourDirectoryName>.onmicrosoft.com/.well-known/openid-configuration
or
https://login.microsoftonline.com/{tenant}/.well-known/openid-configuration
or for v2.0
https://login.microsoftonline.com/{tenant}/v2.0/.well-known/openid-configuration
Inside that file is bunch of url’s containing “TenantID” right after string https://login.windows.net, see figure below
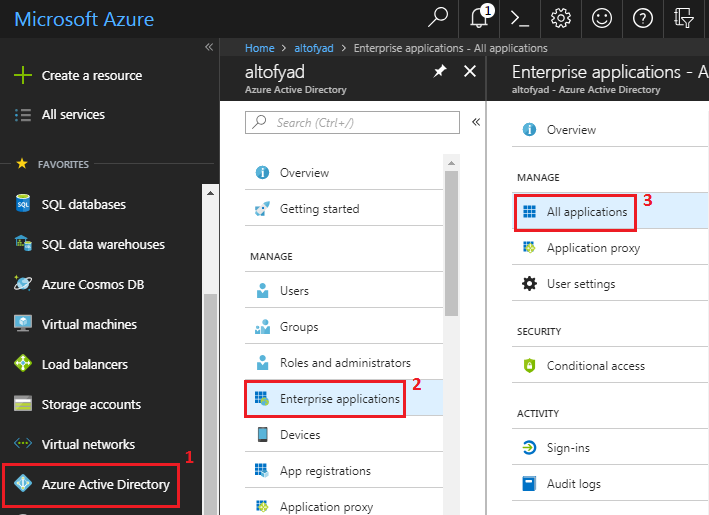
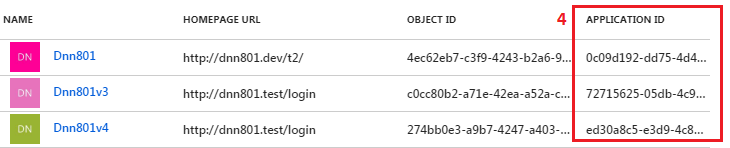
8.3. Application ID¶
The ID of an “Application” which exist in “Azure AD”. “Application ID” is sent to “Azure AD” during authentication to indicate which application the caller wants a token for.
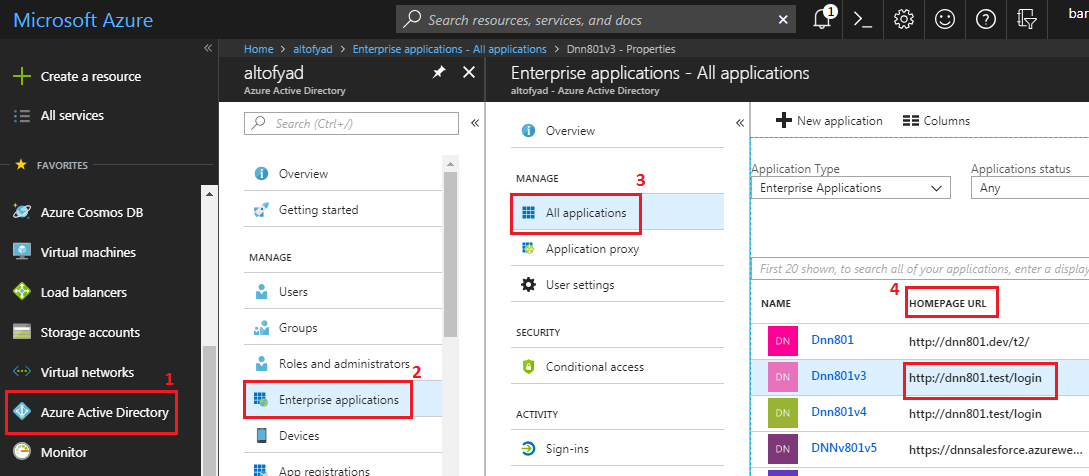
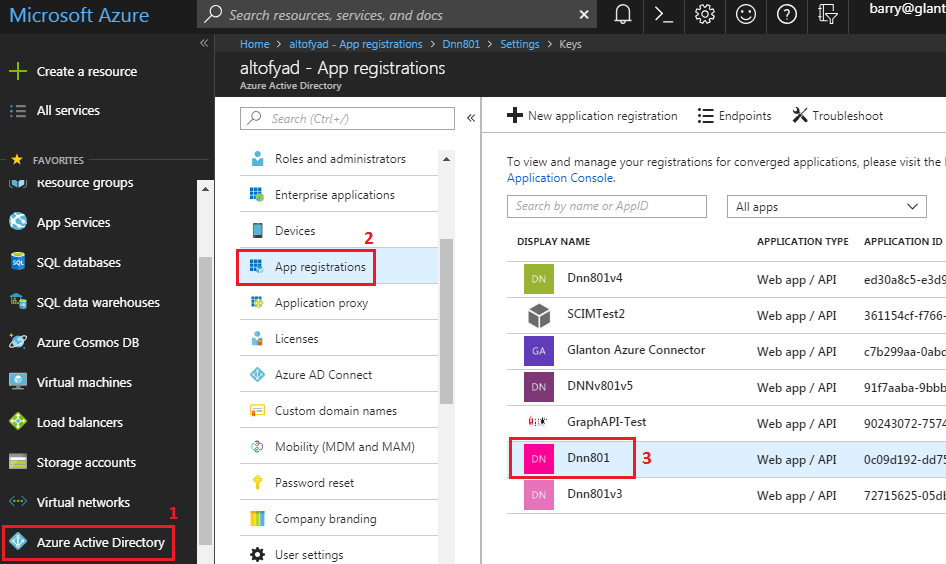
Process of creating “Application” is described in this section. Figures below describes how to obtain “Application ID” if it’s already exist in “Azure AD”.
.
.
8.4. Login page¶
“Login page” is an URL where the user will be redirected to enter his “Azure AD” credentials. Our Azure AD Connector supports two types of login endpoints:
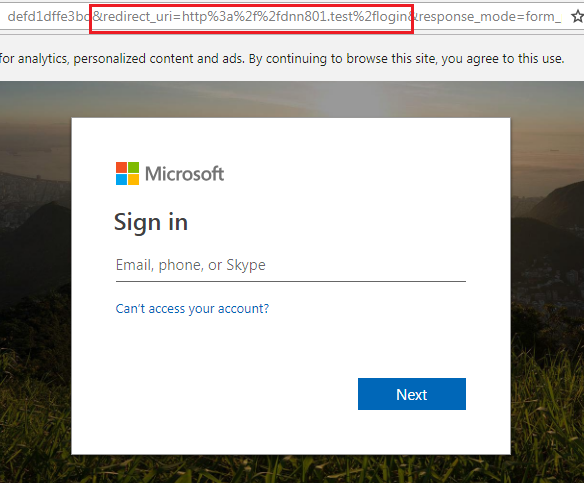
https://login.microsoftonline.com/{0}/v2.0, plugin will automatically replace{0}by the Tenant. Only work or school or students Microsoft accounts, likeuser@{Tenant}.onmicrosoft.comare able to sign in. In other words it would only allow sign-ins from user accounts provisioned in the same tenant as the one where the application is registered. Figure below shows login screen, notice the login page URL on it.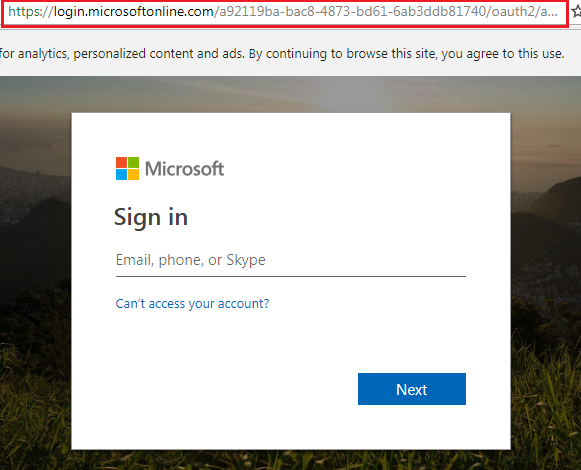
https://login.microsoftonline.com/commonThis allow sign in forMSA- personal Microsoft accounts, in addition to work or school or students Microsoft accounts. People from outside@{Tenant}.onmicrosoft.combe able to authenticate and access DNN (e.g. Skype, Xbox, Outlook.com, Office 365 subscribers).
8.5. Redirect URI¶
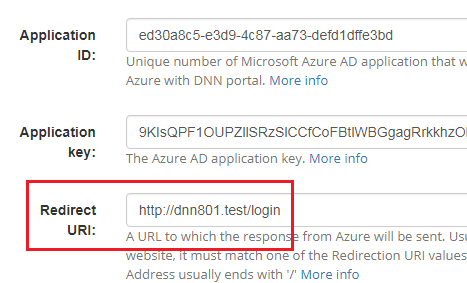
An URI to which the response from “Azure AD” will be sent, eg: security token. “Redirect URI” in “AD-Pro Azure AD Connector” needs to be the same as “HomePage URL” in “Azure AD” Application.
Inside “Azure AD” Application it can be found on behalf of “HomePage URL”, see figure below:
Inside “AD-Pro Azure AD Connector” it’s located under “Azure Settings” tab, on behalf on “Redirect URI” attribute, see figure below:
“Azure AD” login page URL contains this parameter in behalf of key redirect_uri, string is encoded. See figure below:
8.6. Authentication key¶
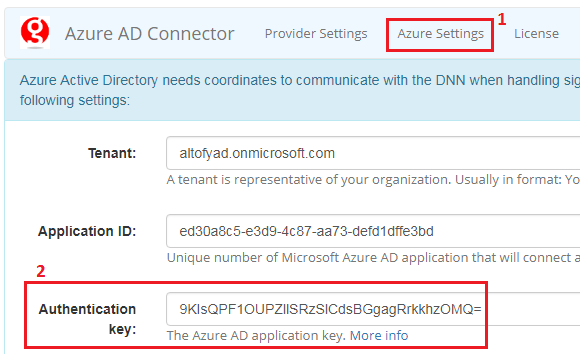
“Authentication key” is a secret string assigned to the “Azure AD” Application. The “Authentication key” along with a “Application ID” is used to authenticate call to the Graph API. You can create multiple keys to address key rollover scenarios. You can delete keys that are expired, compromised, or no longer in use. “Authentication key” in “AD-Pro Azure AD Connector” is located under “Azure Settings”, see figure below:
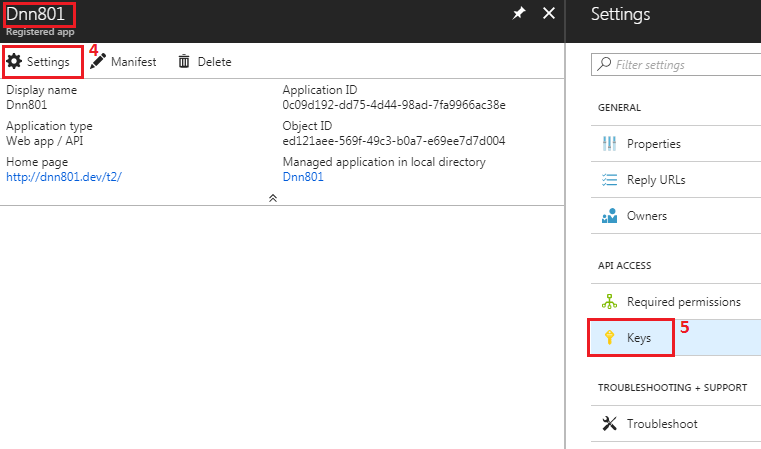
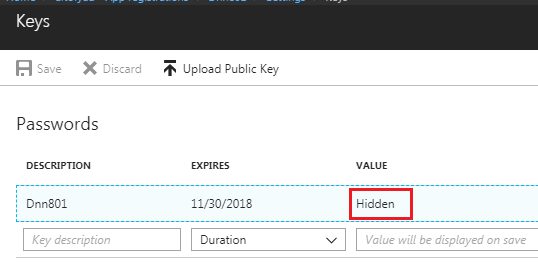
To locate “Authentication key” in “Azure AD” Application, follow steps below:
8.7. OAuth 2.0¶
OAuth is protocol for Authorization (it’s playing with permissions). OAuth is not for Authentication. OAuth 2.0 defines mechanism to obtain and use access token to access protected resources. “Azure AD Connector” is using “OAuth 2.0 authorization code grant flow” to access “Azure AD” resources.
8.8. OpenID Connect¶
OpenID Connect is a simple identity layer built on top of the OAuth 2.0 protocol. (It’a a extension for OAuth 2.0)
- It defines standard methods to provide identity information.
- Implements authentication as an extension to the OAuth 2.0 authorization process.
- Provides information about the end user in the form of an id_token that verifies the identity of the user and provides basic profile information about the user.
- It’s recommendation for a web application that is hosted on a server and accessed via a browser.
OpenID Connect is described by a JSON metadata document. It contains most of the informations required for an DNN to perform sign-in, and it can be found at these locations:
https://login.windows.net/{YourDirectoryName}.onmicrosoft.com/.well-known/openid-configuration- or
https://login.microsoftonline.com/{tenant}/.well-known/openid-configuration - or for v2.0:
https://login.microsoftonline.com/{tenant}/v2.0/.well-known/openid-configuration